#Web3SecurityGuide
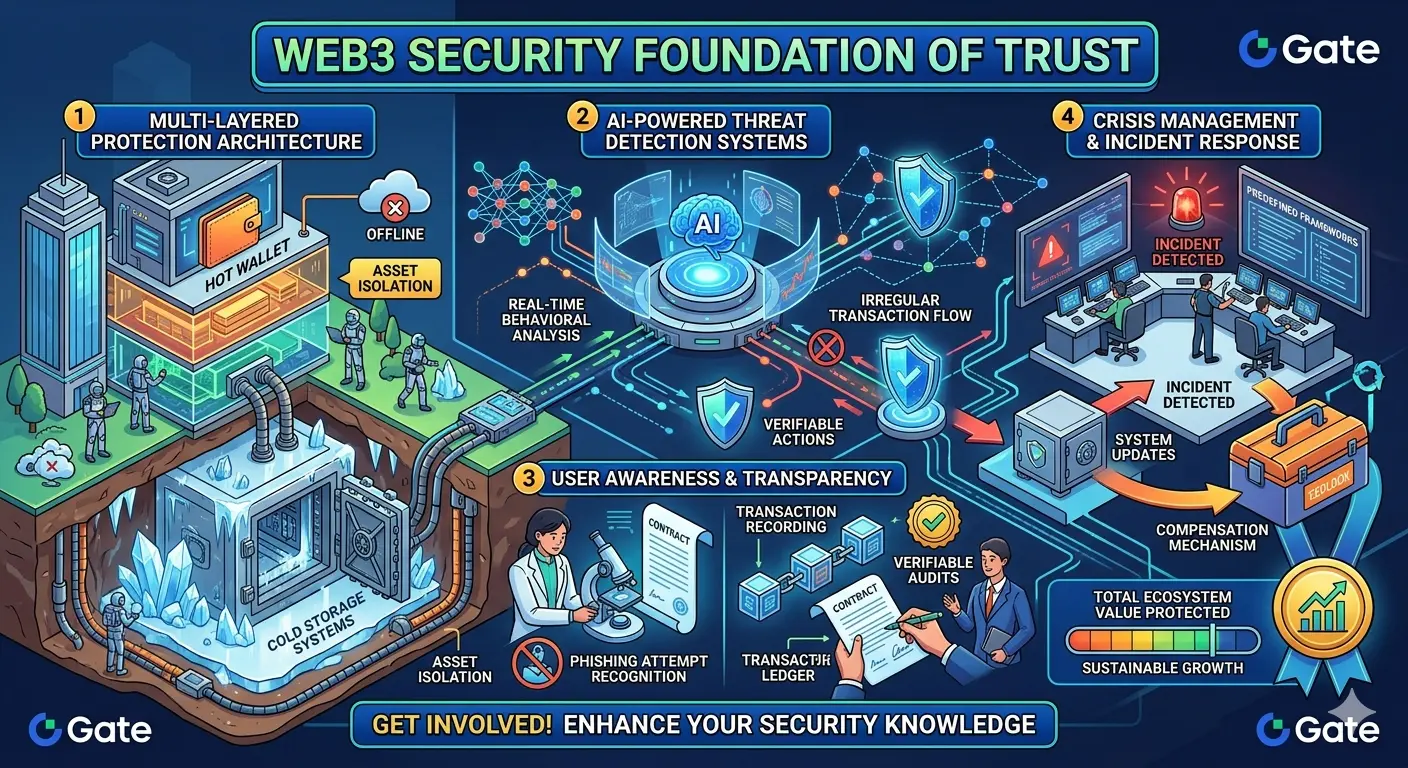
In the cryptocurrency ecosystem, security is not just a technical requirement—it is the foundation of trust that protects users’ digital assets. As the Web3 landscape continues to evolve, security protocols are becoming more sophisticated, adopting layered defense mechanisms designed to minimize risk and enhance resilience against emerging threats.
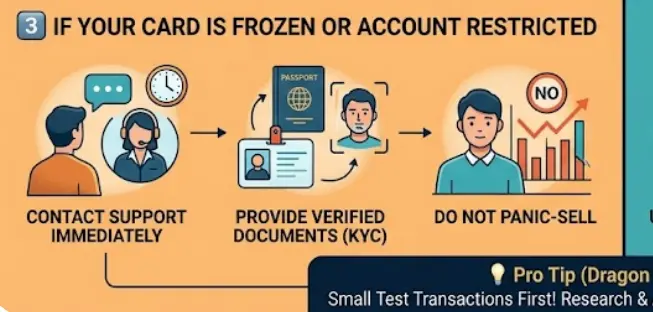
Multi-Layered Protection Architecture
Modern platforms no longer rely on a single line of defense. Instead, they implement a comprehensive, multi-layered security framework.
Cold storage systems play a critical role by keeping the majority of assets in offline environments, isolated from external threats. This hybrid structure ensures that even in extreme scenarios, user funds remain protected through strict segregation and controlled access mechanisms.
AI-Powered Threat Detection Systems
Beyond traditional safeguards, advanced artificial intelligence models are now central to security operations.
These systems continuously analyze behavioral patterns, identifying anomalies in real time. Suspicious activities such as irregular transaction flows or unauthorized access attempts are automatically flagged and mitigated before they escalate into critical incidents.
User Awareness & Transparency
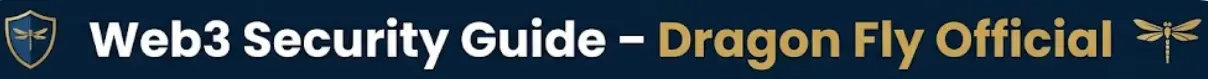
Security is not solely dependent on infrastructure; informed users are an equally important layer of defense.
Educational resources help individuals recognize phishing attempts, malicious interfaces, and deceptive tactics. At the same time, transparent transaction recording and auditability reinforce confidence, ensuring that every action within the system can be verified and traced.
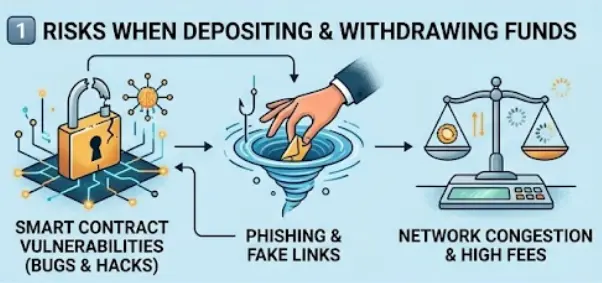
Crisis Management & Incident Response
No system is entirely immune to risk, which is why robust emergency protocols are essential.
Dedicated response teams operate under predefined frameworks to contain potential threats, minimize damage, and maintain operational continuity. Compensation mechanisms and continuous system updates further strengthen long-term reliability.
Conclusion: Security as a Dynamic Process
Web3 security is not a fixed destination—it is an ongoing, adaptive process. The combination of technological innovation and user-centric awareness forms the backbone of a secure digital asset environment.
In this new paradigm, sustainable growth is only possible where security evolves as fast as the ecosystem itself.
In the cryptocurrency ecosystem, security is not just a technical requirement—it is the foundation of trust that protects users’ digital assets. As the Web3 landscape continues to evolve, security protocols are becoming more sophisticated, adopting layered defense mechanisms designed to minimize risk and enhance resilience against emerging threats.
Multi-Layered Protection Architecture
Modern platforms no longer rely on a single line of defense. Instead, they implement a comprehensive, multi-layered security framework.
Cold storage systems play a critical role by keeping the majority of assets in offline environments, isolated from external threats. This hybrid structure ensures that even in extreme scenarios, user funds remain protected through strict segregation and controlled access mechanisms.
AI-Powered Threat Detection Systems
Beyond traditional safeguards, advanced artificial intelligence models are now central to security operations.
These systems continuously analyze behavioral patterns, identifying anomalies in real time. Suspicious activities such as irregular transaction flows or unauthorized access attempts are automatically flagged and mitigated before they escalate into critical incidents.
User Awareness & Transparency
Security is not solely dependent on infrastructure; informed users are an equally important layer of defense.
Educational resources help individuals recognize phishing attempts, malicious interfaces, and deceptive tactics. At the same time, transparent transaction recording and auditability reinforce confidence, ensuring that every action within the system can be verified and traced.
Crisis Management & Incident Response
No system is entirely immune to risk, which is why robust emergency protocols are essential.
Dedicated response teams operate under predefined frameworks to contain potential threats, minimize damage, and maintain operational continuity. Compensation mechanisms and continuous system updates further strengthen long-term reliability.
Conclusion: Security as a Dynamic Process
Web3 security is not a fixed destination—it is an ongoing, adaptive process. The combination of technological innovation and user-centric awareness forms the backbone of a secure digital asset environment.
In this new paradigm, sustainable growth is only possible where security evolves as fast as the ecosystem itself.