Radiant Protocol was hacked and lost $4.5 million within seconds of its launch.
The reason is that in the new USDC market, the mathematical rounding problem in the “burn” function is amplified and exploited, allowing hackers to extract additional USDC.
Compiled by Daniel Tan
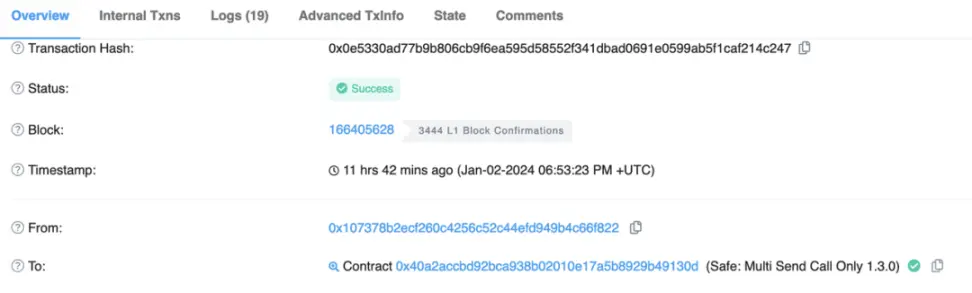
On January 3, 2024, Beijing time, the Radiant protocol on Arbitrum was attacked by flash loans. Hackers conducted 3 attacks on the #Radiant protocol, resulting in a total loss of 1,902 ETH (worth $4.5 million). The root cause is that in the new $USDC market, a mathematical rounding problem in the “burn” function was amplified and exploited, allowing hackers to withdraw additional $USDC.
MetaTrust Labs conducted in-depth research and analysis of this attack, revealing how hackers exploited the vulnerability.
Lending Protocol Radiant Protocol
Radiant is a decentralized, non-custodial lending protocol that runs on multiple chains, including Arbitrum, BNBChain, and Ethereum.
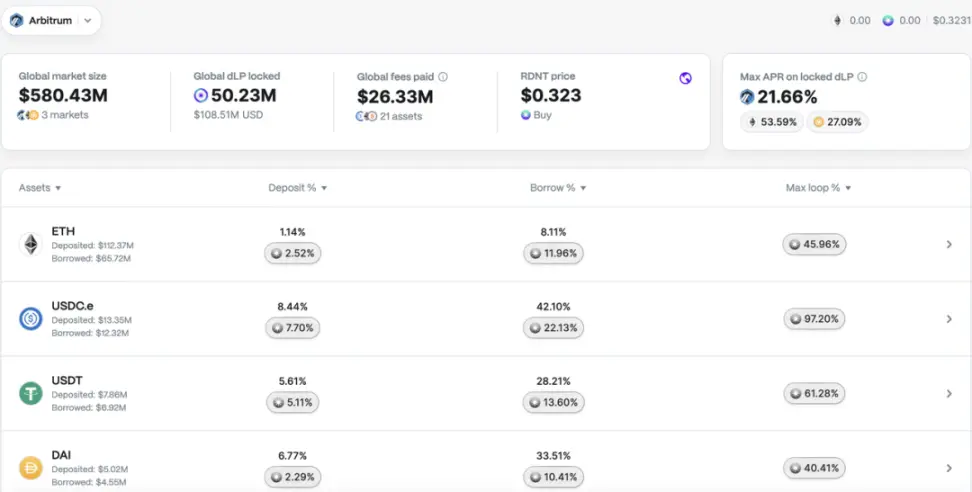
After the attack, the total value locked in the Radiant protocol was still $313 million. This was because the project team quickly suspended the protocol after being attacked to prevent further losses.

timeline

trade
0xc5c4bbddec70edb58efba60c1f27bce6515a45ffcab4236026a5eeb3e877fc6d
0x2af556386c023f7ebe7c662fd5d1c6cc5ed7fba4723cbd75e00faaa98cd14243
0x1ce7e9a9e3b6dd3293c9067221ac3260858ce119ecb7ca860eac28b2474c7c9b
Asset Loss
The three attack transactions resulted in a total loss of more than 1,902 ETH, worth more than 4.5 million US dollars. At the time of writing, 1,902 $ETH were still stored in the hacker’s wallet (0x826d5f4d8084980366f975e10db6c4cf1f9dde6d).
attacker
0x826d5f4d8084980366f975e10db6c4cf1f9dde6d
Attack Contract
0x39519c027b503f40867548fb0c890b11728faa8f
Contract under attack
Radiant: Lending Pool:
0xf4b1486dd74d07706052a33d31d7c0aafd0659e1
rUSDCn:
0x3a2d44e354f2d88ef6da7a5a4646fd70182a7f55
What happened before the attack
Fifteen seconds before the attack, the project party had just created a new USDC market on Arbitrum, and the hacker was the first person to interact with the new USDC market.
Attack Steps
Take the first attack transaction 0x1ce7e9a9e3b6dd3293c9067221ac3260858ce119ecb7ca860eac28b2474c7c9b as an example.
-
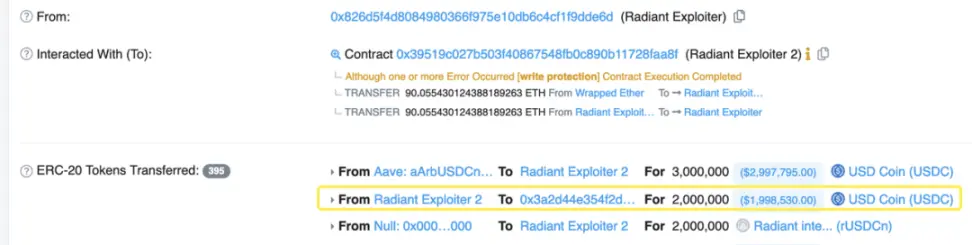
Borrow USD 3 million USDC from AAVE through the flash loan function;
-
Deposit 2M $USDC into Radiant Pool. At this time, the liquidityIndex is 1e27.
-
Make a $2 million flash loan on Radiant Lending Pool and enlarge the liquidityIndex to 1.8e36.
-
Repeat step 3, 151 times, to enlarge the liauidityIndex to 2.7e38, which is 270000000000 times the initial value.
-
Borrow 90.6 $ETH from Radiant Pool, worth $215K. This is the profit from this attack;
-
Create a new contract (0xd8b591);
-
Approve the unlimited USDC for the new contract, transfer 543K $USDC to the new contract, and use the new contract to perform the following steps; transfer 543K $USDC to the new contract, and use the new contract to perform the following steps;
-
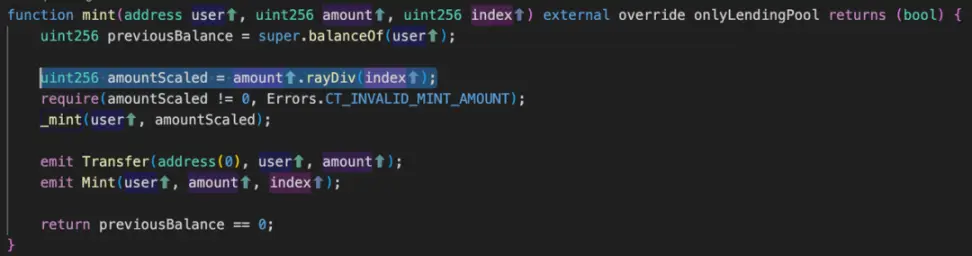
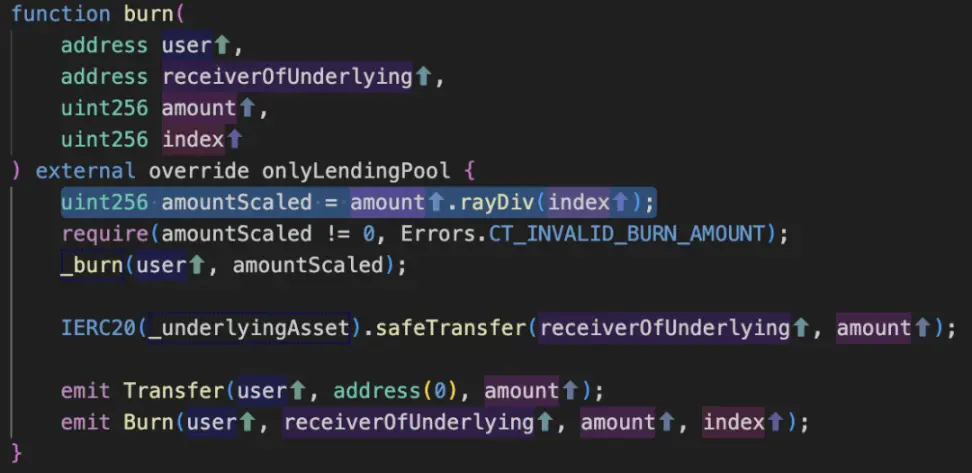
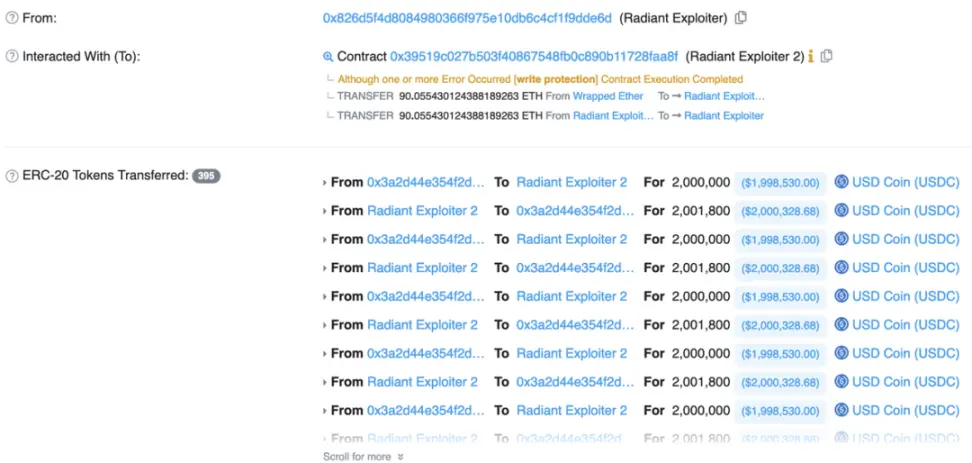
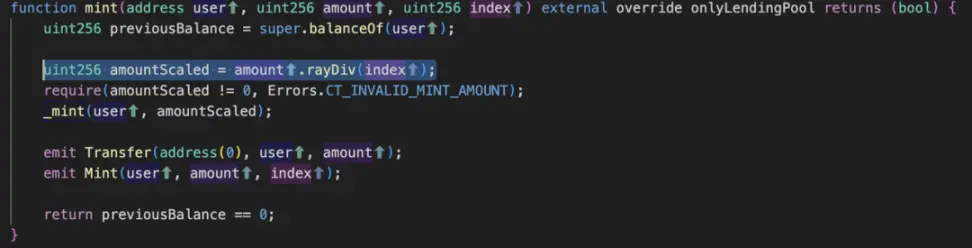
Deposit 543K $USDC into the Radiant pool and mint 2 wei tokens. Because the amountScaled is 2 tokens, 543600000002*1e27/271800000000999999999999998631966035920=2;

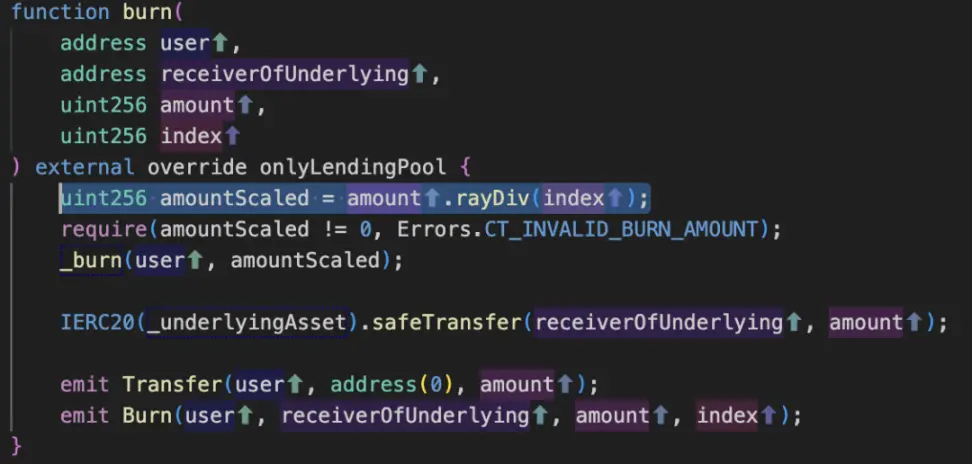
- Withdrawing 407K $USDC from the Radiant pool, burning only 1 wei of tokens because amountScaled is 1, 407700000000*1e27/2718000000009999999999999998631966035920=1.5 and mathematical rounding issues. Please note that amountScaled is a uint256 type variable, which will convert 1.5 to 1.

-
Deposit 271K $USDC into the Radiant pool and mint tokens with an amountScaled of 1 because 271800000001*1e27/271800000000999999999999998631966035920=1
-
Withdraw 407K $USDC from the Radiant pool and only destroy tokens with an amountScaled of 1.
-
Repeat steps 10 and 11 up to 18 times and drain the $USDC from the new market that the hacker previously deposited into the new market.
-
Convert 2 $WETH to 4.73K $USDC and 3.23K $USDC to 1.36 $WETH.
-
Use USD 3.5 million USDC as the principal and USD 15,000 USDC as the fee to repay AAVE’s flash loan.
-
Profit of $90 ETH.
root cause
The fundamental reason is that the hacker was the first to interact with the newly created native USDC market, exploited the Radiant protocol’s flash loan function to amplify the liquidityIndex, and exploited mathematical rounding problems to steal assets from the lending pool.
Key code