Aztec Network Architecture Explained: Sequencer, Prover, and the Noir Programming Model
As the Ethereum ecosystem evolves, Rollup has emerged as the leading solution for scaling performance. Both Optimistic Rollup and zkRollup share the primary goal of reducing costs and boosting throughput. However, most Layer2 solutions still inherit Ethereum’s transparency—making all trades and status data publicly accessible.
While this model was acceptable in DeFi’s early days, the increasing complexity of on-chain applications has made privacy an essential demand. Users want to hide trading strategies, enterprises seek to protect business data, and institutions must balance privacy with compliance. The introduction of Aztec marks a pivotal shift, transforming Rollup from a “scaling tool” into a “privacy execution environment.”
Industry Position and Significance of Aztec Architecture
Most projects in the current zkRollup space focus on performance and EVM compatibility. Aztec, however, takes a different approach—embedding privacy as a foundational element of its architecture. Rather than simply optimizing trade processing, Aztec redefines how Smart Contracts are executed.
This positions Aztec closer to a “privacy operating system” than a conventional scaling solution. By leveraging private execution, zero-knowledge proofs, and a dedicated programming language, Aztec empowers developers to create applications that are both verifiable and privacy-preserving.
From an industry perspective, this architecture opens new horizons for Web3 applications—including privacy-centric finance, on-chain identity, and enterprise-grade blockchain solutions. Understanding Aztec’s network architecture is key to grasping the future of blockchain infrastructure.
Overview of Aztec Network Architecture
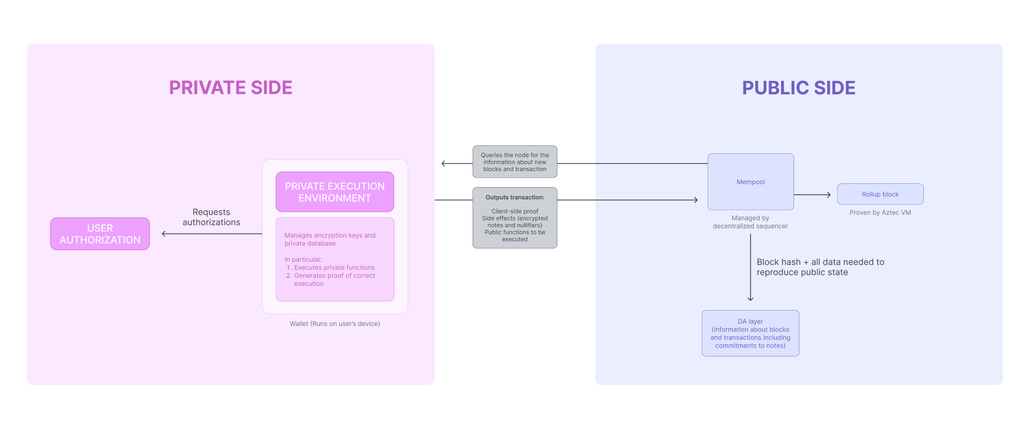
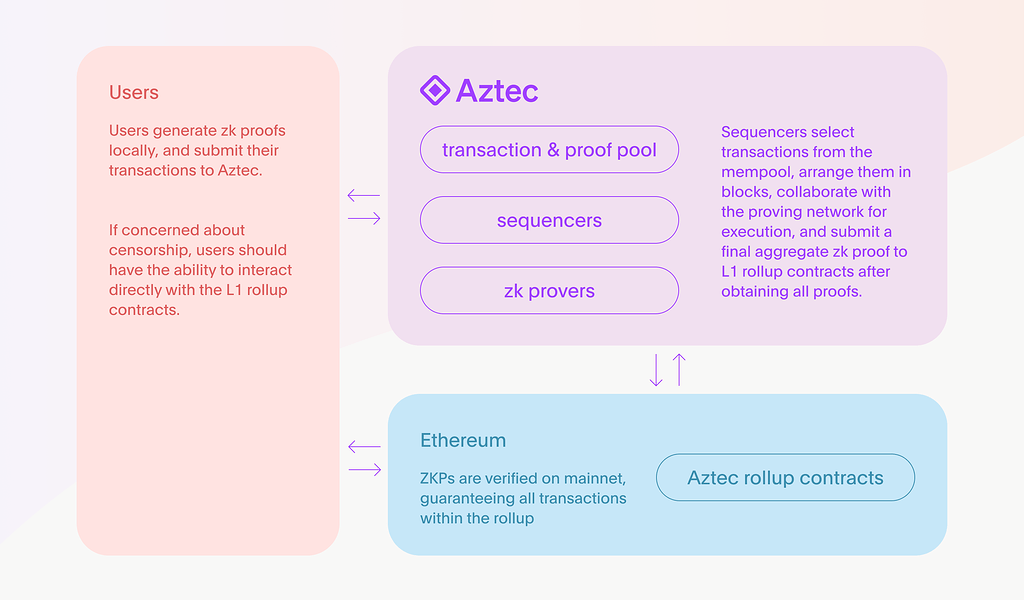
Aztec’s core architecture is a coordinated system of three primary modules: Sequencer, Prover, and the Noir programming model. These modules correspond to trade processing, proof generation, and developer interfaces, respectively.
Sequencer Selection Overview | Source: Aztec
Here’s how the process works: after a user initiates a trade, the Sequencer sorts and packages it; the Prover then generates zero-knowledge proofs for these trades; finally, these proofs are submitted to the Ethereum mainnet for verification. Throughout this process, Noir defines privacy logic and contract behavior, giving developers control over data visibility.
This layered design enables Aztec to deliver high performance, robust privacy, and strong programmability.
Sequencer: Trade Ordering and Block Construction
The Sequencer is the central coordinator in the Aztec network. Its primary role is to receive user trades, sort them, and package them into Layer2 blocks.
Like traditional blockchains, the Sequencer determines the order of trade execution. In Aztec, however, it also handles encrypted status updates and private execution results. This means the Sequencer doesn’t directly access trade content; instead, it organizes trades based on encrypted data.
The Sequencer also submits trading data to the proof system and updates the final status on Ethereum. Its efficiency directly impacts the network’s throughput and user experience.
From a design perspective, the Sequencer is critical to performance but is not a trust anchor—final correctness is always guaranteed by zero-knowledge proofs.
Prover: The Core of Zero-Knowledge Proof Generation
The Prover acts as Aztec’s “security engine,” responsible for generating zkSNARK proofs for trade execution. Its core function is to prove to Ethereum that a batch of trades was executed correctly, without revealing any sensitive details.
All computation results in Aztec must ultimately be converted into verifiable mathematical proofs by the Prover. Since this process is computationally intensive, the Prover’s performance and optimization are vital.
Importantly, the Prover is not a single node—it can be a network of multiple participants. This design boosts decentralization and helps distribute the computational workload.
With the Prover, Aztec achieves a crucial feature: even when all data is encrypted, the system remains fully verifiable.
Noir: Aztec’s Privacy Programming Model
Noir is Aztec’s dedicated zero-knowledge programming language, designed to lower the barrier for developers building privacy-focused applications. Unlike Solidity, Noir is built from the ground up for private execution.
Developers using Noir can define which variables are private and which are public, compiling this logic directly into zero-knowledge circuits. Privacy is thus an integral part of application logic—not an afterthought.
The introduction of Noir transforms Aztec from a simple execution environment into a comprehensive development platform. Developers can build private Smart Contracts without deep expertise in cryptography.
Long-term, Noir has the potential to become a standard tool for zero-knowledge application development.
How Do These Three Components Work Together?
In practice, Sequencer, Prover, and Noir are tightly integrated rather than isolated systems.
When a user initiates a trade through a Noir-based application, the trade is first executed privately on the user’s device, generating encrypted status updates. The Sequencer then sorts and packages these trades, the Prover generates zero-knowledge proofs for the entire block, and the proof is submitted to Ethereum for verification and settlement.
This workflow achieves a critical objective: enabling trusted computation and status updates without exposing sensitive data.
In essence, Aztec doesn’t just “hide data”—it establishes a comprehensive privacy computing framework.
Summary
Aztec’s network architecture represents a paradigm shift in blockchain design, integrating privacy, verifiability, and programmability through the collaboration of Sequencer, Prover, and Noir. This approach not only solves the privacy limitations of traditional blockchains but also establishes a robust foundation for next-generation Web3 applications.
FAQs
Is the Sequencer in Aztec centralized?
Currently, the Sequencer may exhibit some degree of centralization, but this does not compromise system security since zero-knowledge proofs guarantee final status correctness. Aztec plans to gradually move toward decentralized sequencing in the future.
Will the Prover become a performance bottleneck?
The Prover’s computations are complex, but efficiency can be significantly improved through parallelization and specialized hardware. Building a network of Provers is also a key strategy for addressing performance challenges.
What is the difference between Noir and Solidity?
Noir is purpose-built for zero-knowledge proofs, with a focus on privacy and circuit generation. Solidity, by contrast, is designed for traditional public Smart Contracts. The two languages differ fundamentally in design philosophy and use cases.
Does Aztec support migration of existing Ethereum applications?
Because Aztec’s execution environment is not fully EVM-compatible, existing applications require some refactoring—especially in terms of privacy logic.
Why does Aztec need a dedicated programming language?
Privacy computing requires intricate zero-knowledge circuit design, which would be highly complex in traditional programming languages. Noir was created to make privacy application development more intuitive and efficient for developers.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


