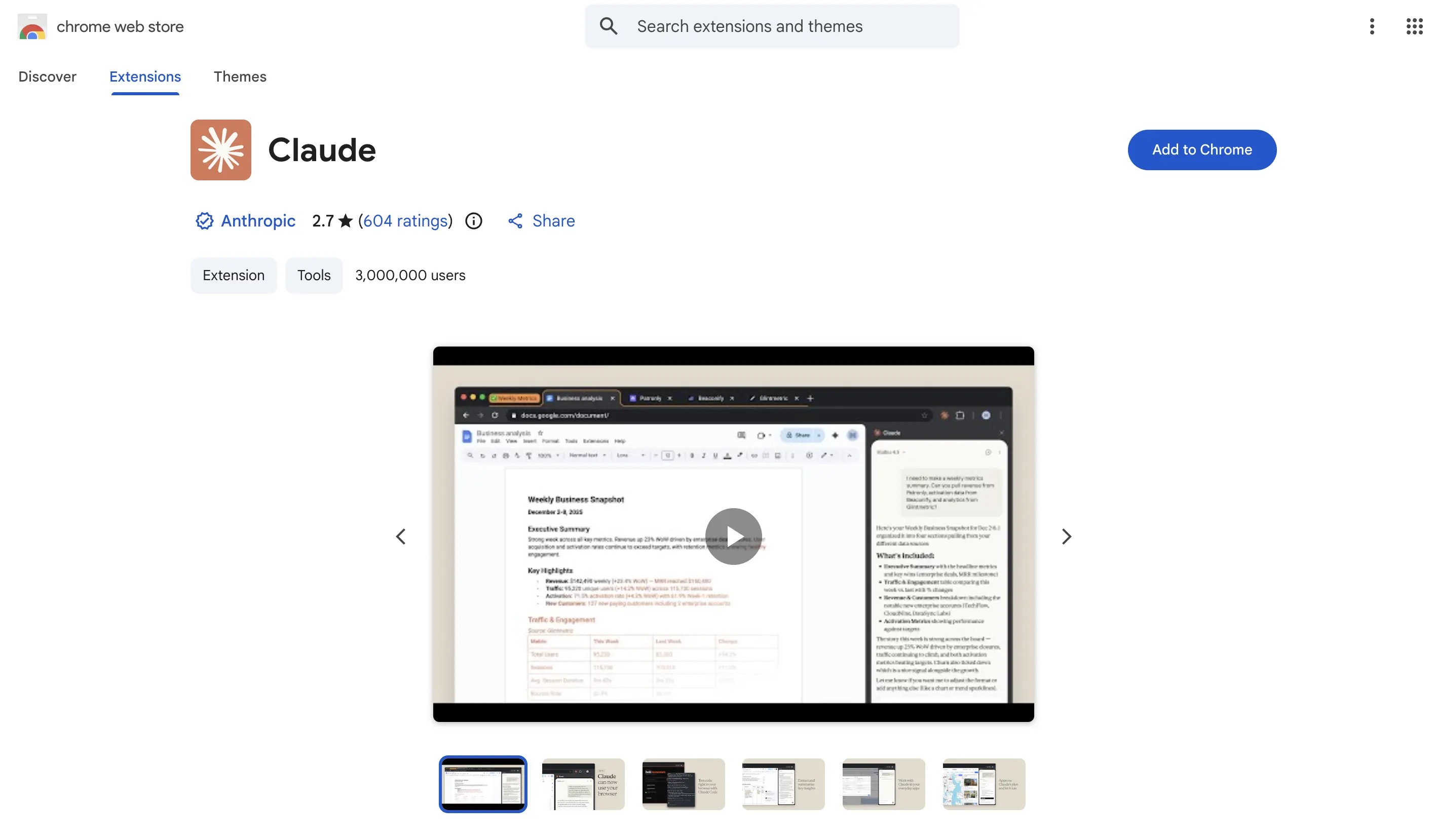
安全監控平台 GoPlus 於 3 月 27 日發出高危警報,指出 Anthropic Claude Chrome 瀏覽器擴充功能存在高危 Prompt 注入漏洞,影響低於 1.0.41 版本的安裝,覆蓋用戶超過 300 萬。攻擊者可讀取 Google Drive 文件、竊取業務 Token 並以用戶身分發送電子郵件。
漏洞原理:兩個弱點結合形成完整攻擊鏈
此次漏洞由兩個獨立的安全缺陷組合後構成高危攻擊路徑。
第一個弱點:Claude Chrome 擴充功能的過寬子網域信任 Claude Chrome 擴充功能的訊息傳遞機制允許來自所有 *.claude.ai 子網域的指令通過,其中一個訊息類型 onboarding_task 可直接接受外部 Prompt 並交由 Claude 執行,未設置更精細的來源驗證。
第二個弱點:Arkose Labs 驗證碼元件的 DOM-based XSS 漏洞 Anthropic 使用第三方驗證碼供應商 Arkose Labs,其 CAPTCHA 元件託管於 a-cdn.claude.ai——一個屬於 *.claude.ai 信任範圍的子網域。安全研究人員在舊版 CAPTCHA 元件中發現一個 DOM-based XSS 漏洞:元件接收外部訊息時從未驗證發送者身分(未檢查 event.origin),且將用戶可控字串直接渲染為 HTML,未進行任何清理處理。
完整攻擊鏈路:受害者訪問惡意網頁 → 後台靜默加載含 XSS 漏洞的 Arkose iframe → 注入惡意 Payload 在 a-cdn.claude.ai 域內執行 → 利用子網域信任白名單向 Claude 擴充功能發送惡意 Prompt 並自動執行。整個過程在不可見的隱藏 iframe 中完成,受害者完全無從察覺。
攻擊者能做什麼:帳號被無感知完全接管
一旦攻擊成功,攻擊者可對受害者帳號執行以下操作,且全程不需任何使用者授權或點擊:
· 竊取 Gmail 存取權令牌(可持久化訪問 Gmail、聯絡人)
· 讀取 Google Drive 中的所有文件
· 匯出 Claude 完整聊天記錄
· 以受害者身分發送電子郵件
· 在後台建立新標籤頁、開啟 Claude 側邊欄並執行任意指令
修復狀態與安全建議
此漏洞已完成全面修復:Anthropic 於 2026 年 1 月 15 日修補 Claude Chrome 擴充功能,新版本僅允許來自 的請求通過;Arkose Labs 於 2026 年 2 月 19 日修復 XSS 漏洞,全面複測於 2026 年 2 月 24 日確認問題解決。GoPlus 此次警報旨在提醒仍使用舊版本的用戶及時升級。
GoPlus 提出以下安全建議:前往 Chrome 瀏覽器的 chrome://extensions,找到 Claude 擴充程序,確認版本號碼為 1.0.41 或以上;警惕來自不明來源的釣魚鏈接;AI Agent 應用應遵循「最小權限原則」;涉及高敏感操作時應引入人工二次確認(Human-in-the-loop)機制。
常見問題
如何確認我的 Claude Chrome 擴充功能版本是否安全?
前往 Chrome 瀏覽器的 chrome://extensions,找到 Claude 擴充程序並查看版本號碼。若版本為 1.0.41 或以上,漏洞已修復;若低於 1.0.41,請立即更新或重新安裝最新版本。
此漏洞需要用戶主動點擊惡意連結才會觸發嗎?
不需要。只要用戶訪問了惡意網頁,攻擊即可在後台靜默執行,無需任何點擊、授權或確認操作。整個攻擊鏈在隱藏的 iframe 中完成,受害者完全無法察覺。
Anthropic 已完成修復,為何仍需更新?
部分用戶可能未開啟瀏覽器擴充功能的自動更新,導致仍在使用低於 1.0.41 的舊版本。GoPlus 的警報旨在提醒這部分用戶主動確認版本並手動升級,以確保安全。
Disclaimer: The information on this page may come from third parties and does not represent the views or opinions of Gate. The content displayed on this page is for reference only and does not constitute any financial, investment, or legal advice. Gate does not guarantee the accuracy or completeness of the information and shall not be liable for any losses arising from the use of this information. Virtual asset investments carry high risks and are subject to significant price volatility. You may lose all of your invested principal. Please fully understand the relevant risks and make prudent decisions based on your own financial situation and risk tolerance. For details, please refer to
Disclaimer.
Articoli correlati
JPMorgan: DeFi Security Exploits and Stagnant TVL Limit Institutional Adoption
Gate News message, April 23 — JPMorgan analysts led by managing director Nikolaos Panigirtzoglou said that persistent decentralized finance (DeFi) exploits and weak growth continue to limit institutional interest in the sector. The recent Kelp DAO hack wiped approximately $20 billion from DeFi's tot
GateNews4h fa
U.S. Treasury Sanctions Cambodian Senator Over Crypto Scam Network
## Overview
The U.S. Treasury Department sanctioned Cambodian Senator Kok An and 28 entities associated with him on Thursday, according to the Treasury's Office of Foreign Assets Control (OFAC). The action targets what officials describe as a massive crypto scam operation in Southeast Asia.
## The
CryptoFrontier4h fa
Aave Freezes rsETH Reserves Across Five Networks Following KelpDAO Exploit
Gate News message, April 23 — Aave has frozen rsETH reserves across Ethereum Core, Arbitrum, Base, Mantle, and Linea as the recovery effort accelerates following the April 18 KelpDAO exploit that drained 116,500 rsETH, valued at approximately $292 million, from Kelp's cross-chain bridge.
Multiple D
GateNews6h fa
摩根大通:DeFi 駭客頻傳與 TVL 停滯壓縮機構興趣,資金轉投 USDT
摩根大通報告認為DeFi持續漏洞、跨鏈橋與預言機攻擊頻繁,致TVL停滯、削弱機構投資意願,資金轉向可追蹤、可凍結的USDT。KelpDAO與Rhea Finance攻擊揭示風控風險,中心化穩定幣與托管更受青睞;長期要改善需超越保險與治理,DeFi難回到2021年高TVL,穩定幣將更集中。
ChainNewsAbmedia6h fa
Circle Chief Economist Proposes Raising USDC Rates on Aave Amid KelpDAO Fallout
Gate News message, April 23 — Gordon Liao, Circle's chief economist, has proposed raising USDC lending parameters on Aave v3 Ethereum Core this week following a $292 million KelpDAO rsETH exploit that triggered a liquidity crisis across the protocol. Liao's Request for Comment suggests increasing "S
GateNews7h fa
Major CEX Upgrades Fraud Detection System with Machine Learning and Rule Engine, Cuts Response Time to Hours
Gate News message, April 23 — A major centralized exchange announced an overhaul of its anti-fraud system by integrating machine learning models with rule-based engines, implementing a dual-track strategy where models handle long-term defense and rules enable rapid response. The unified framework
GateNews7h fa